When a major retail business moves to shutter its operations the impacts have major reverberations, especially when that business is the size of Circuit City, Borders Books and Music, or Toys “R” Us. In the case of the latter, the rapid closing of the toy giant left 31,000 employees without work and close to 800 properties vacant. When any business chooses (or is forced) to close, there’s always a great deal of uncertainty, and simple things tend to get overlooked. There’s also the potential for disgruntled employees to simply ignore standard operating procedures or, worse, ignore regulations regarding personally identifiable information (PII) and create a massive data security problem in the process.
Arghman / iStock / Getty Images Plus / Getty Images
In an interesting read posted on Hackaday, Tom Nardi outlines his recent trip to a closed-up Toys “R” Us location. His visit was on the level; his friend’s company had purchased the property, and they were doing a walk-through before the scrappers and demolition teams came through to take the place apart. Of course, he jumped at the chance.
Nardi was surprised by what remained after the liquidation sale and the auction for furnishings and equipment. In sum, he calls the trip “a very surprising look at what gets left behind when the money runs out and the employees simply give up.”
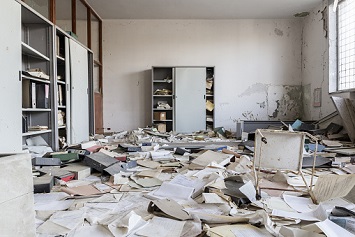
The store looks “post-apocalyptic,” with puddles of water on the floor; checkout lines with only partial point-of-sale systems remaining; junk and boxes scattered on the floor; and plenty of other things. In the store security area, there still was a functioning system, though it looked like more than a few of the cameras had been broken, knocked over, or otherwise jostled during the shutdown.
We start to get a glimpse of the impending security issues in the manager’s office: There were a large number of keys and lock cores laid out on the desk, and there was an open box on the desk detailing “the comings and goings of cash from the armored car service.” The large safe was left open, though it was obviously empty. Surprisingly, though, it appeared to have the safe combo taped either to the door or, at the very least, to the outside of the safe. A big security no-no.
The Records Room
From a security perspective, here’s where things get really bad. Nardi and friends entered another room, separate from the manager’s office, and what they found was pretty shocking: numerous open boxes and file cabinet drawers filled with folder upon folder of sensitive employee records relating to their hiring, work history, medical information, tax and payroll information, and even photocopies of I-9 documents such as a driver’s license and Social Security card. You can scroll through the images here.
According to Nardi, one employee’s file was laying open on the desk, with the scan of her license and Social Security card on top and a sticky note containing her phone number and work availability written on it.
The implementation of numerous data breach regulations such as the General Data Protection Regulation (GDPR) and the California Consumer Protection Act (CCPA) reflect the overall cultural shift toward protecting PII. Regardless of the behavior of individual management and workers at the closing location, the company has obligations it must meet with regard to protecting employees’ PII, including the retention and handling of sensitive documents when a business shuts down.
At the end of the day, a company’s HR and security teams are responsible for protecting this information and ensuring that the management at individual locations is in compliance with the applicable regulations governing PII handling. If unsure, you can start by checking with the Internal Revenue Service or the Small Business Administration, both of which have online guides to get you started. Should you need further guidance, there are more in-depth, interactive resources, such as those found at hr.blr.com.
